Perché usare HTTPS?
I browser contrassegnano i siti non HTTPS come "Non sicuri": questo è solo uno dei tanti buoni motivi per proteggere un sito Web.
Obiettivi di apprendimento
Dopo aver letto questo articolo sarai in grado di:
- Descrivere le modifiche al traffico HTTPS
- Spiegare i miti di HTTPS e la verità
- Capire i motivi per cui utilizzare HTTPS
Argomenti correlati
Vuoi saperne di più?
Abbonati a theNET, il riepilogo mensile di Cloudflare sulle tematiche più discusse in Internet.
Copia link dell'articolo
Qual è la differenza tra HTTP e HTTPS?
HTTPS è HTTP con crittografia TLS. HTTPS utilizza TLS (SSL) per crittografare le normali richieste e risposte HTTP, rendendolo più sicuro e protetto. Un sito Web che utilizza HTTPS ha https:// all'inizio del suo URL anziché http://, come https://www.cloudflare.com.
Quindi, perché i siti Web dovrebbero utilizzare HTTPS?
Motivo n. 1: i siti Web che utilizzano HTTPS sono più affidabili per gli utenti.
Un sito web che utilizza HTTPS è come un ristorante che espone un "Pass" dell'ispettore locale per la sicurezza alimentare: i potenziali clienti possono essere certi di poter frequentare l'attività senza subire conseguenze negative. E al giorno d'oggi, usare l'HTTP è sostanzialmente come esporre un cartello di controllo di sicurezza alimentare con la dicitura "No pass": non c'è alcuna garanzia che non accada qualcosa di terribile a un cliente.
HTTPS utilizza il protocollo SSL/TLS per crittografare le comunicazioni, impedendo agli aggressori di rubare i dati. SSL/TLS conferma inoltre che il server di un sito Web è effettivamente chi dice di essere, impedendo così le impersonificazioni. In questo modo si bloccano molteplici tipi di attacchi informatici (proprio come la sicurezza alimentare previene le intossicazioni).
Anche se alcuni utenti potrebbero non essere a conoscenza dei vantaggi di SSL/TLS, i browser moderni si assicurano di essere consapevoli dell'affidabilità di un sito Web in ogni caso.
Chrome e altri browser contrassegnano tutti i siti web HTTP come "non sicuri".
Nel corso degli anni, Google ha adottato misure graduali per incoraggiare i siti Web a integrare HTTPS. Google utilizza HTTPS anche come fattore di qualità nel modo in cui restituisce i risultati di ricerca: più è sicuro il sito Web, minore è la probabilità che il visitatore commetta un errore cliccando sul link fornito da Google.
A partire da luglio 2018, con il rilascio di Chrome 68, tutto il traffico HTTP non protetto è stato contrassegnato nella barra degli URL come "non sicuro". Questa notifica viene visualizzata per tutti i siti Web privi di un certificato SSL valido. Altri browser hanno seguito l'esempio.
Motivo n. 2: HTTPS è più sicuro, sia per gli utenti che per i proprietari di un sito Web.
Con HTTPS, i dati vengono crittografati durante il transito in entrambe le direzioni: in entrata e in uscita dal server di origine. Il protocollo mantiene le comunicazioni sicure in modo che i malintenzionati non possano osservare quali dati vengono inviati. Di conseguenza, i nomi utente e le password non possono essere rubati in transito, quando ad esempio gli utenti li inseriscono in un modulo. Se i siti Web o le applicazioni Web devono inviare dati sensibili o personali agli utenti (ad esempio, informazioni sui conti bancari), la crittografia protegge anche tali dati.
Motivo n. 3: HTTPS autentica i siti Web.
Gli utenti di app di ridesharing come Uber e Lyft non devono necessariamente salire su un'auto sconosciuta per fiducia, solo perché l'autista dice di essere lì per venirli a prendere. Le app invece forniscono informazioni sul conducente, come il nome, l'aspetto, il tipo di auto che guida e il numero di targa. L'utente può controllare queste cose ed essere certo di salire sull'auto giusta, anche se ogni auto in condivisione è diversa e non ha mai visto il conducente prima.
Allo stesso modo, quando un utente naviga su un sito Web, quello che sta facendo è connettersi a computer lontani di cui non è a conoscenza, gestiti da persone che non ha mai visto. Un certificato SSL, che abilita HTTPS, è simile alle informazioni del conducente nell'app di ridesharing. Rappresenta la verifica esterna da parte di una terza parte affidabile che un server Web è chi afferma di essere.
In questo modo si prevengono gli attacchi in cui un malintenzionato impersona o falsifica un sito Web, facendo credere agli utenti di trovarsi sul sito che intendevano visitare, quando in realtà si trovano su un sito falso. Anche l'autenticazione HTTPS contribuisce notevolmente a far apparire legittimo un sito Web aziendale, influenzando l'atteggiamento degli utenti nei confronti dell'azienda stessa.
Miti e concezioni HTTPS
Molti siti Web sono stati lenti ad adottare HTTPS. Per capire perché, dobbiamo analizzare la storia.
Quando HTTPS iniziò a essere implementato, l'implementazione corretta era difficile, lenta e costosa; era difficile da distribuire correttamente, rallentava le richieste Internet e aumentava i costi perché richiedeva costosi servizi di certificazione. Nessuno di questi impedimenti è ancora reale, ma per molti proprietari di siti Web persiste una paura persistente, che ha impedito ad alcuni di loro di fare il grande passo verso una maggiore sicurezza. Esploriamo alcuni dei falsi miti su HTTPS.
"Non gestisco informazioni sensibili sul mio sito Web, quindi non ho bisogno di HTTPS"
Un motivo comune per cui i siti Web non implementano la sicurezza è perché pensano che sia eccessivo per i loro scopi. Dopotutto, se non hai a che fare con dati sensibili, a chi importa se qualcuno sta spiando? Ci sono alcune ragioni per cui questa è una visione eccessivamente semplicistica della sicurezza Web. Ad esempio, alcuni provider di servizi Internet inseriscono addirittura pubblicità nei siti Web gestiti tramite HTTP. Questi annunci potrebbero essere in linea o meno con il contenuto del sito Web e potrebbero risultare offensivi, a parte il fatto che il fornitore del sito Web non ha alcun contributo creativo né partecipa ai ricavi. Una volta che un sito è protetto, non è più possibile inserire annunci pubblicitari non autorizzati.
I browser Web moderni ora limitano le funzionalità dei siti che non sono sicuri. Funzionalità importanti che migliorano la qualità del sito Web ora richiedono HTTPS. La geolocalizzazione, le notifiche push e i worker di servizi necessari per eseguire le applicazioni Web progressive (PWA) richiedono tutti un livello di sicurezza elevato. Ciò ha senso: dati come la posizione di un utente sono sensibili e possono essere utilizzati per scopi nefasti.
"Non voglio danneggiare le prestazioni del mio sito Web aumentando i tempi di caricamento delle pagine"
Le prestazioni sono un fattore importante sia per l'esperienza dell'utente che per il modo in cui Google restituisce i risultati nelle ricerche. È quindi comprensibile che l'aumento della latenza sia qualcosa da prendere sul serio. Fortunatamente, nel corso del tempo sono stati apportati miglioramenti al protocollo HTTPS per ridurre il sovraccarico di prestazioni necessario per impostare una connessione crittografata.
Quando si verifica una connessione HTTP, sono diversi i passaggi che la connessione deve effettuare tra il client che richiede la pagina Web e il server. Oltre alla normale latenza associata a un handshake TCP (mostrato in blu di seguito), per utilizzare HTTPS deve verificarsi un ulteriore handshake TLS/SSL (mostrato in giallo).
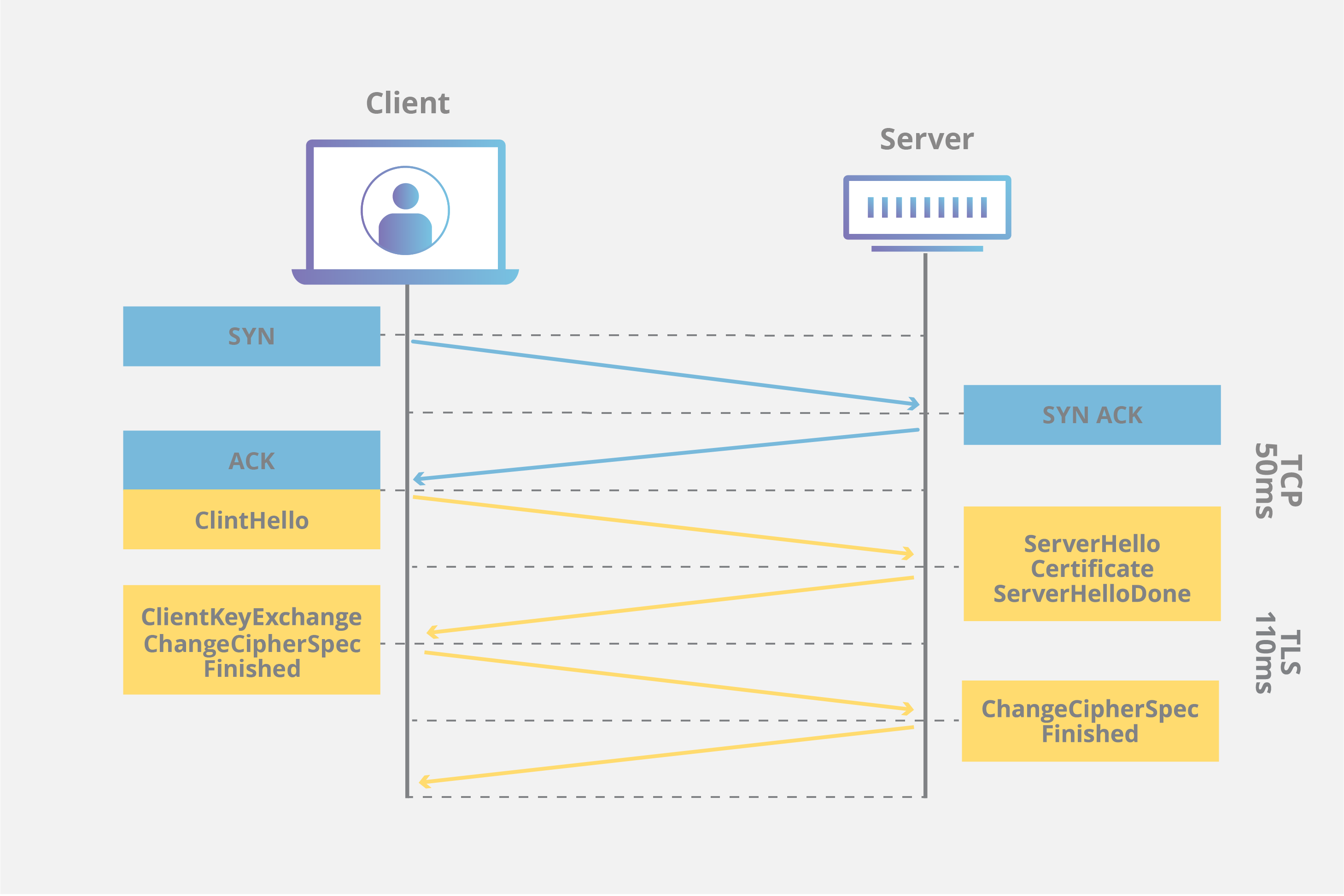
Sono stati implementati miglioramenti in TLS per ridurre la latenza totale di creazione di una connessione, inclusa la ripresa della sessione TLS e il falso avvio TLS.
Utilizzando la ripresa della sessione, un server può mantenere attiva una connessione più a lungo, riprendendo la stessa sessione per richieste aggiuntive. Mantenere attiva la connessione consente di risparmiare tempo nella rinegoziazione della connessione quando il client richiede un recupero dell'origine non memorizzato nella cache, riducendo l'RTT totale del 50%.
Un altro miglioramento alla velocità con cui è possibile creare un canale crittografato è l'implementazione di un processo denominato falso avvio TLS, che riduce la latenza inviando i dati crittografati prima che il client abbia completato l'autenticazione. Per ulteriori informazioni scopri come funziona TLS/SSL su una CDN.
Infine, TLS 1.3 offre miglioramenti delle prestazioni ancora più significativi. Gli handshake TLS in TLS 1.3 richiedono solo un viaggio di andata e ritorno e, se il client si è connesso in precedenza, addirittura zero. La registrazione a Cloudflare semplifica l'attivazione di TLS 1.3 per una proprietà Web.
"Implementare HTTPS è troppo costoso per me"
Un tempo questo poteva essere vero, ma ora il costo non è più un problema: Cloudflare offre ai siti Web la possibilità di crittografare gratuitamente il transito. Siamo stati i primi a fornire SSL gratuitamente e continuiamo a farlo. Migliorando la sicurezza Internet in generale, siamo in grado di contribuire a rendere Internet più sicuro e veloce.
"Perderò il posizionamento nei risultati di ricerca durante la migrazione del mio sito a HTTPS"
La migrazione di un sito Web comporta dei rischi e, se eseguita in modo improprio, potrebbe avere un impatto negativo sulla SEO. Tra le potenziali insidie rientrano tempi di inattività del sito Web, pagine Web non scansionate e penalizzazione per duplicazione di contenuti quando sono presenti due copie del sito contemporaneamente. Detto questo, i siti Web possono essere migrati in modo sicuro su HTTPS seguendo le best practice.
Due delle pratiche di migrazione più importanti sono:
1) l'uso dei reindirizzamenti 301 e 2) il corretto posizionamento dei tag canonici. Utilizzando i reindirizzamenti del server 301 sul sito HTTP per puntare alla versione HTTPS, un sito web comunica a Google di passare alla nuova posizione per tutti gli scopi di ricerca e indicizzazione. Inserendo i tag canonici solo sul sito HTTPS, i crawler come Googlebot sapranno che in futuro il nuovo contenuto sicuro dovrà essere considerato canonico.
Se hai un gran numero di pagine e temi che la nuova scansione richieda troppo tempo, contatta Google e comunicagli quanto traffico sei disposto a indirizzare sul tuo sito Web. Gli ingegneri della rete aumenteranno quindi la velocità di scansione per analizzare rapidamente il tuo sito e indicizzarlo.