Our approach to abuse
Cloudflare offers security and reliability services to millions of websites, helping prevent online abuse and make the Internet more secure. When it comes to reports of abuse on websites that use our services, our ability to respond depends on the type of Cloudflare service at issue. Most abuse reports we receive pertain to websites that use our pass-through security and content delivery network (CDN) services, while far fewer reports relate to websites using our registrar services or our services to host content at the edge. Because Cloudflare offers a variety of Internet infrastructure services to users, our abuse reporting system is designed with those different services in mind.
How infrastructure services differ from other Internet services
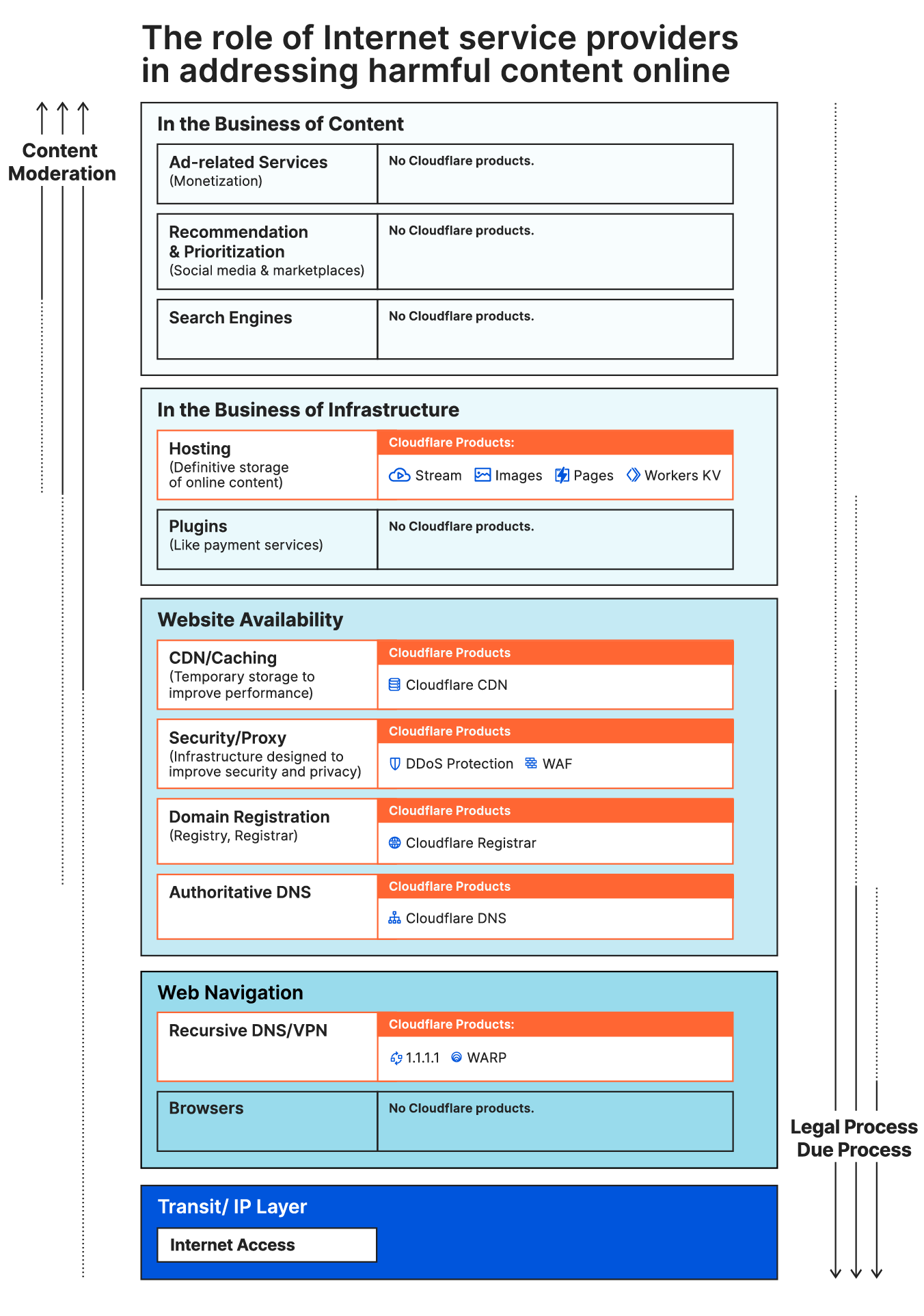
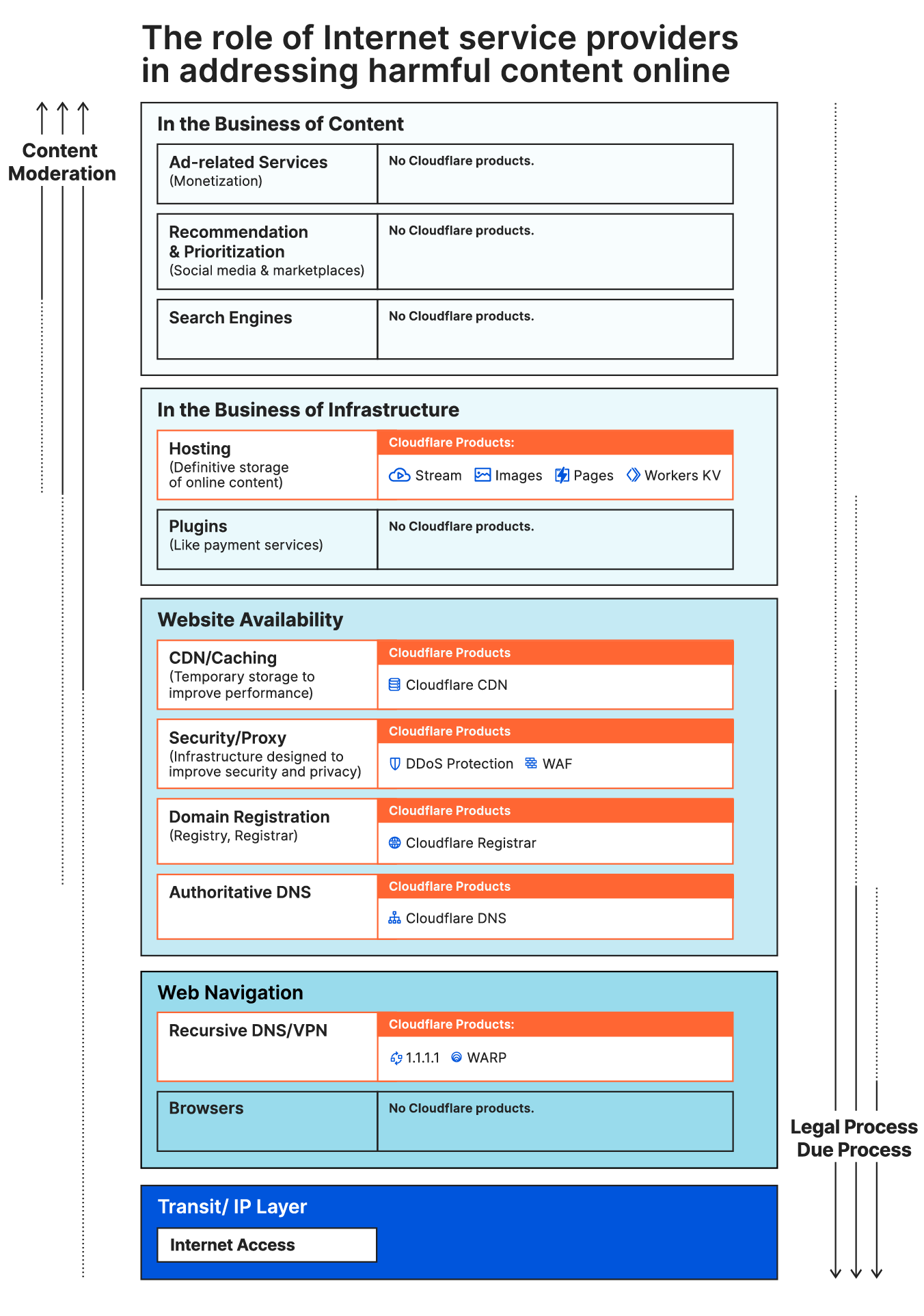
Cloudflare’s approach to abuse reflects the nature of our infrastructure services, which are fundamentally distinct from services like social media platforms and search engines that are designed to interact with and curate content. While content curator services are designed around moderating content, infrastructure services operate without content-based distinction to help make the Internet function more securely, efficiently, and reliably. These differences can be visualized in a stack, where services at the top of the stack are better positioned to address abuse in the first instance.
Everyone benefits from a well-functioning Internet infrastructure, just like other physical infrastructure, and we believe that infrastructure services should generally be made available in a content-neutral way. That is particularly true for services that protect users and customers from cyber attacks.
Cloudflare’s abuse reporting system is designed to ensure that abuse complaints related to content can be addressed by those service providers higher in the stack, and to identify those instances in which action lower down the stack is appropriate.
Why the Cloudflare service at issue matters
Even within the category of Internet infrastructure, different types of services have different abilities to address abusive content. While a hosting provider may be able to effectively remove particular content from a website, other services involved in the transmission of content generally cannot. In addition to being ineffective, attempts to address abuse through cybersecurity services can have unintended consequences and make the broader Internet less secure. Laws like the United States' Digital Millennium Copyright Act and the EU’s Digital Services Act reflect this reality by creating a framework for addressing abuse that distinguishes among hosting services, caching services, and mere conduit services.
Which Cloudflare service(s) are at issue
If you are submitting an abuse report to us because our IP address appears in the WHOIS and DNS records for a website, it is very likely that the website is one of millions of websites that use our pass-through security and content distribution network (CDN) services. Our IP address appears in the WHOIS and DNS records for those websites because of the nature of our security services. If a website uses Cloudflare’s registrar services, that will be reflected in the WHOIS records for the website. If Cloudflare might qualify as the origin hosting provider because of the use of services such as Cloudflare Stream, Cloudflare Pages, Cloudflare Workers, Cloudflare Workers KV, and Cloudflare Images that can definitively store content, our systems will account for those services in processing your report.
Reverse proxy, pass-through security, and CDN services
The vast majority of abuse reports that we receive are about websites using our pass-through security, and content distribution network (CDN) services. Cloudflare does not host content through those services, and we cannot remove content from the Internet that we do not host.
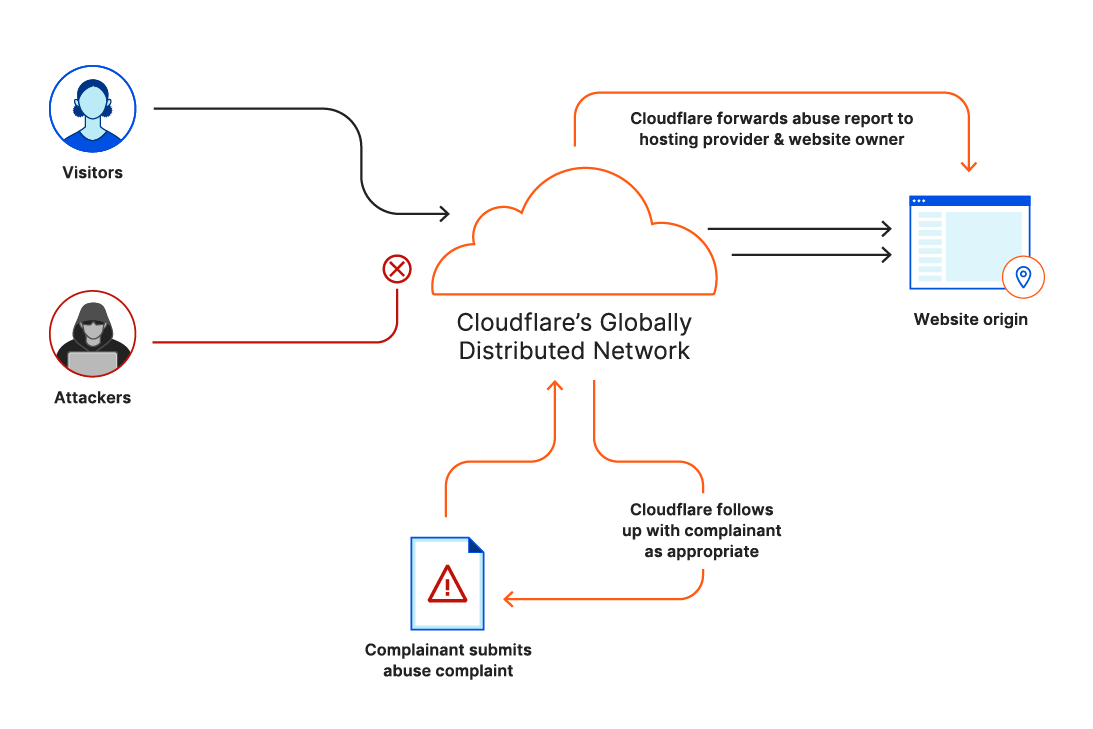
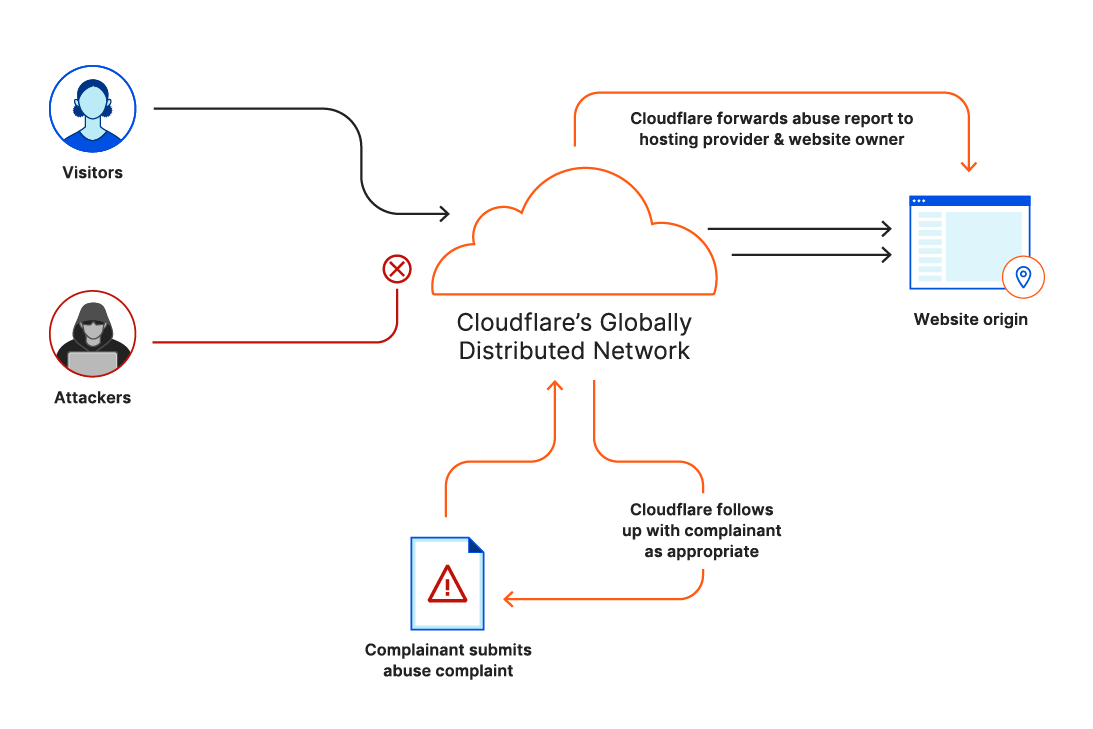
Our abuse reporting system is therefore designed to ensure that your report gets to the parties best positioned to address your complaint: the website operator and the hosting provider for the website on which the content is posted. When you submit a report relating to a website using these services, we will take the following steps:
- Forward your complaint to the website operator and the hosting provider to allow them to take action on it. For some categories of complaints, you can direct us not to forward your complaint to the website operator;
- Provide the hosting provider with the origin IP address of the content at issue to help them locate it;
- Depending on the nature of your complaint, respond to you with additional details so that you can follow up as necessary.
Hosting services
A small minority of abuse reports we receive relate to content definitively stored through Cloudflare Stream, Cloudflare Pages, Cloudflare Workers, Cloudflare Workers KV, or Cloudflare Images such that Cloudflare might qualify as the origin hosting provider. If your abuse report pertains to content that we host and that we believe violates the applicable supplemental terms of service, we will remove or disable access to that content. If we disable access or remove content in response to an abuse report, we generally also notify the website operator of our action and we may make the content available again if appropriate based on the website operator’s response. For certain abuse categories, including copyright and trademark, we follow the notice-and-takedown process set forth in the Digital Millennium Copyright Act. Cloudflare provides notice to the user of steps to remove or limit access to the content. If the user submits a valid counter notice and the abuse reporter fails to initiate a lawsuit, Cloudflare will restore access to the content.
Our Transparency Report includes details on the requests we receive to disable access to content stored on our network, described as “hosted content.”
We may block or remove any content we determine:
- Contains, displays, distributes, or encourages the creation of child sexual abuse material, or otherwise exploits or promotes the exploitation of minors;
- Infringes on intellectual property rights;
- Has been determined by appropriate legal process to be defamatory or libelous;
- Engages in the unlawful distribution of controlled substances;
- Facilitates human trafficking or prostitution in violation of the law;
- Contains, installs, or disseminates any active malware, or uses our platform for exploit delivery (such as part of a command and control system);
- Is otherwise illegal, harmful, or violates the rights of others, including content that discloses sensitive personal information, incites or exploits violence against people or animals, or seeks to defraud the public.