Cloudflare named in Gartner® Magic Quadrant™ for SSE for 2nd year.
Announcement >
Learn
What is Zero Trust Network Access (ZTNA) and what does it do? Read more in our Learning Center. What is ZTNA?
Cloudflare Access
Fast, reliable Zero Trust Network Access (ZTNA)
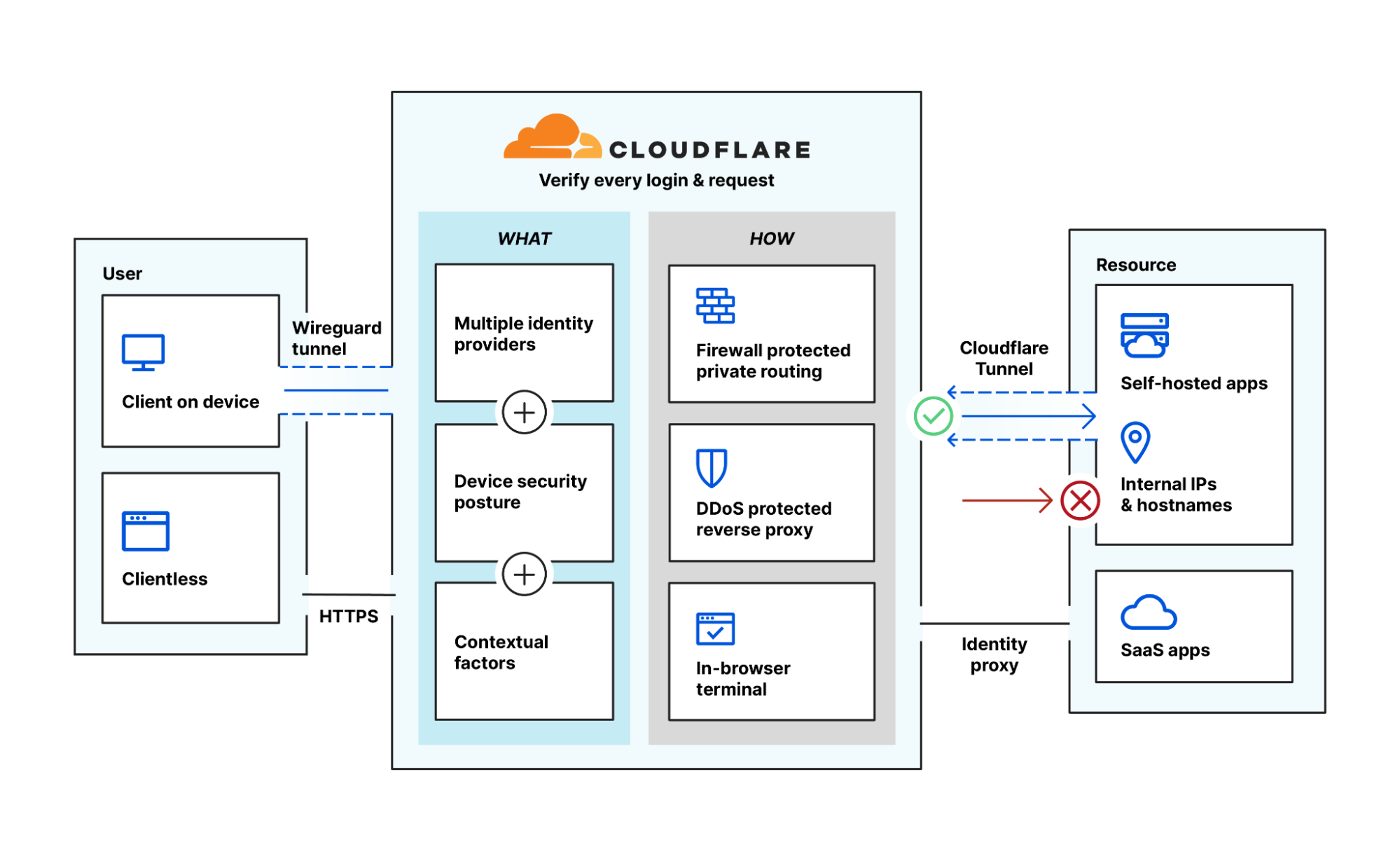
Access verifies context (like identity and device posture) to secure access across your entire environment — no VPN required.
Secure hybrid work
Top use cases for Access

- VPN replacement - Access is faster and safer than traditional VPNs. Start offloading critical apps for better security and end user experience.
- Accelerate mergers & acquisitions - Avoid a traditional network merge entirely. Integrate with multiple IdPs and provide per-app internal access during M&A.
- Contractor access - Authenticate third-party users like contractors with clientless options, social IdPs, and more.
- Developer access - Provide privileged technical users secure access to critical infrastructure without performance tradeoffs.
- Phishing-resistant MFA - Roll out strong authentication, like FIDO2-compliant security keys, everywhere.

Tackle Zero Trust one step at a time
Connect users to internal resources
How it works
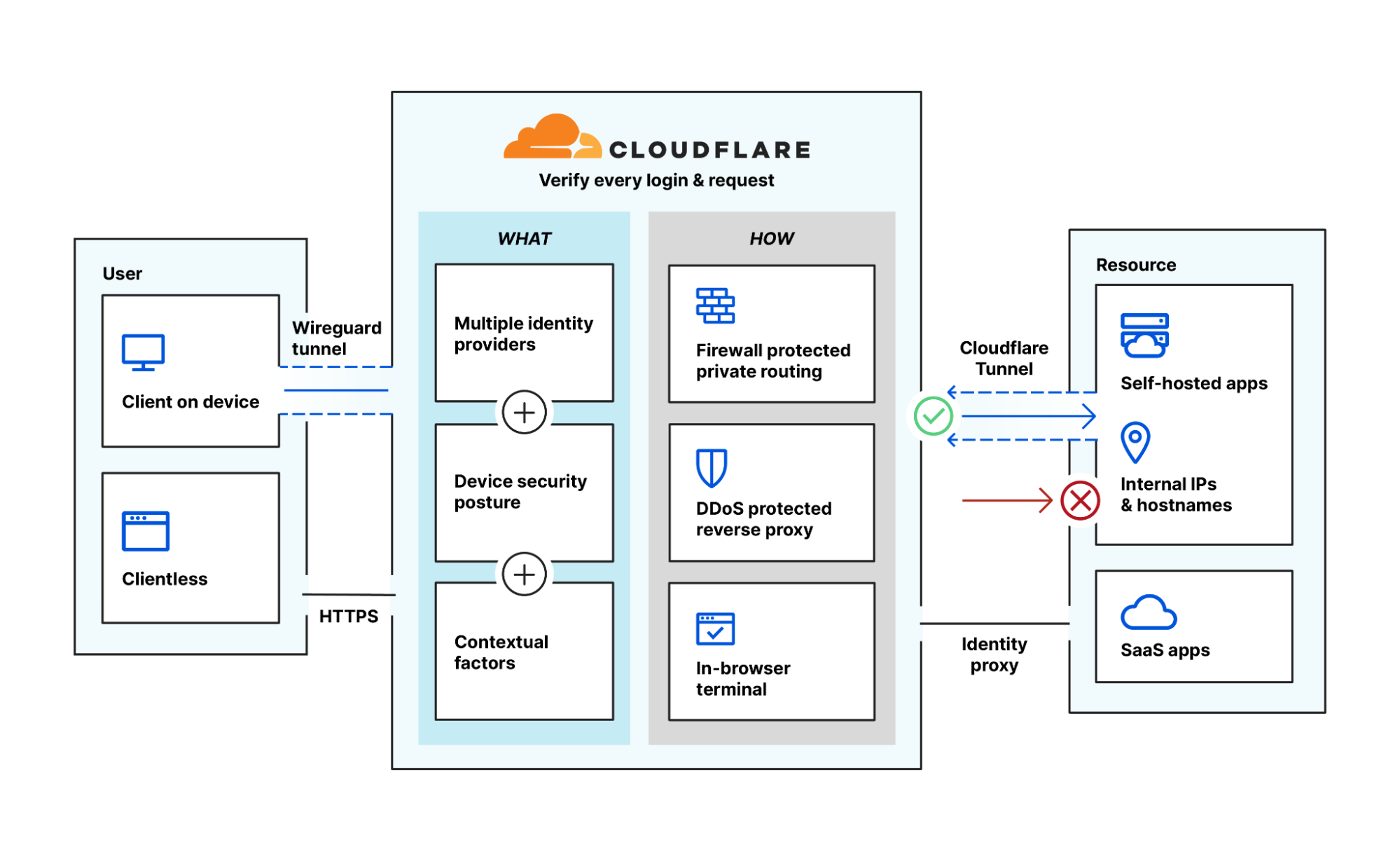
- Clientless capabilities support HTTPS traffic and in-browser SSH or VNC terminals, while our device client can help evaluate device posture or extend traffic to other in-line services like Cloudflare Gateway
- Access verifies identity and device posture and grants continuous, contexual access to all of an organization's internal resources, creating a software-defined perimeter
- In-line WAF and DDoS threat mitigation further strengthen L7 security for apps protected behind Access