Zero Trust Network Access (ZTNA)
Protect what’s yours with a zero-overhead approach to Zero Trust
Securing the corporate perimeter is hard. Embracing Zero Trust security principles should be easy. Start with Zero Trust Network Access (ZTNA), and give your entire ecosystem of users faster, safer access to your corporate resources.
Zero Trust Network Access
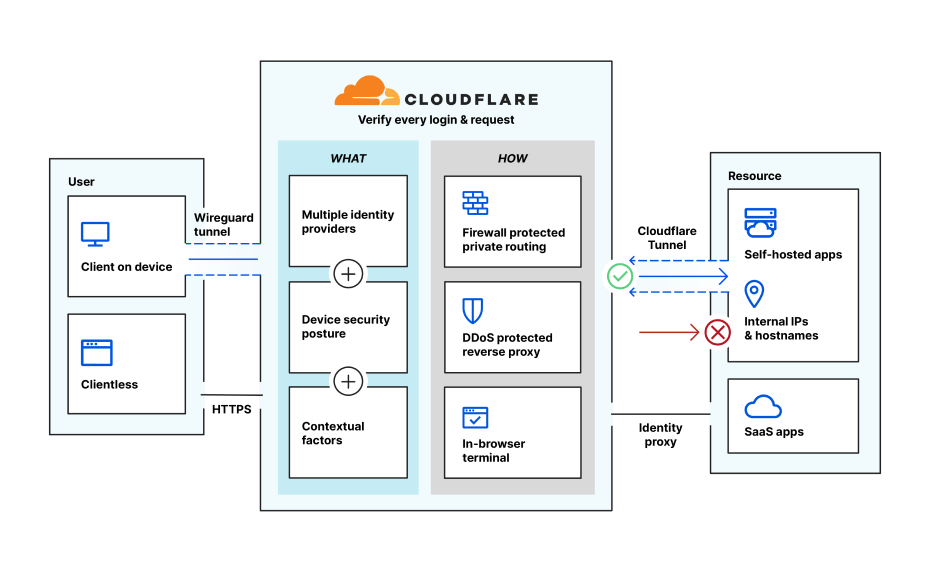
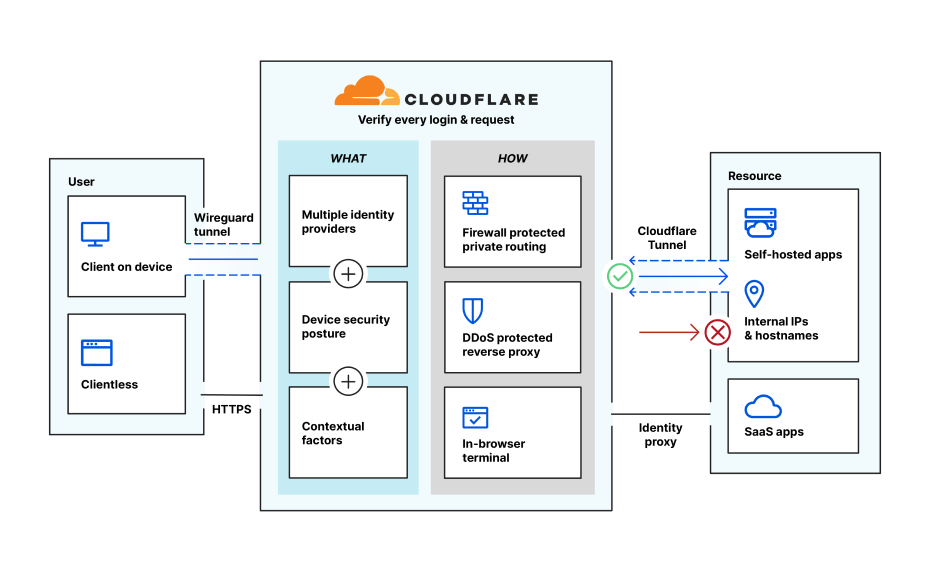
Zero Trust Network Access (ZTNA) technologies create secure boundaries around applications. When resources are protected with ZTNA, users are only allowed to access resources after verifying the identity, context, and policy adherence of each specific request.
Protect internal assets without a VPN
ZTNA replaces VPN connections with universal policies that grant access based on a user’s identity and context.
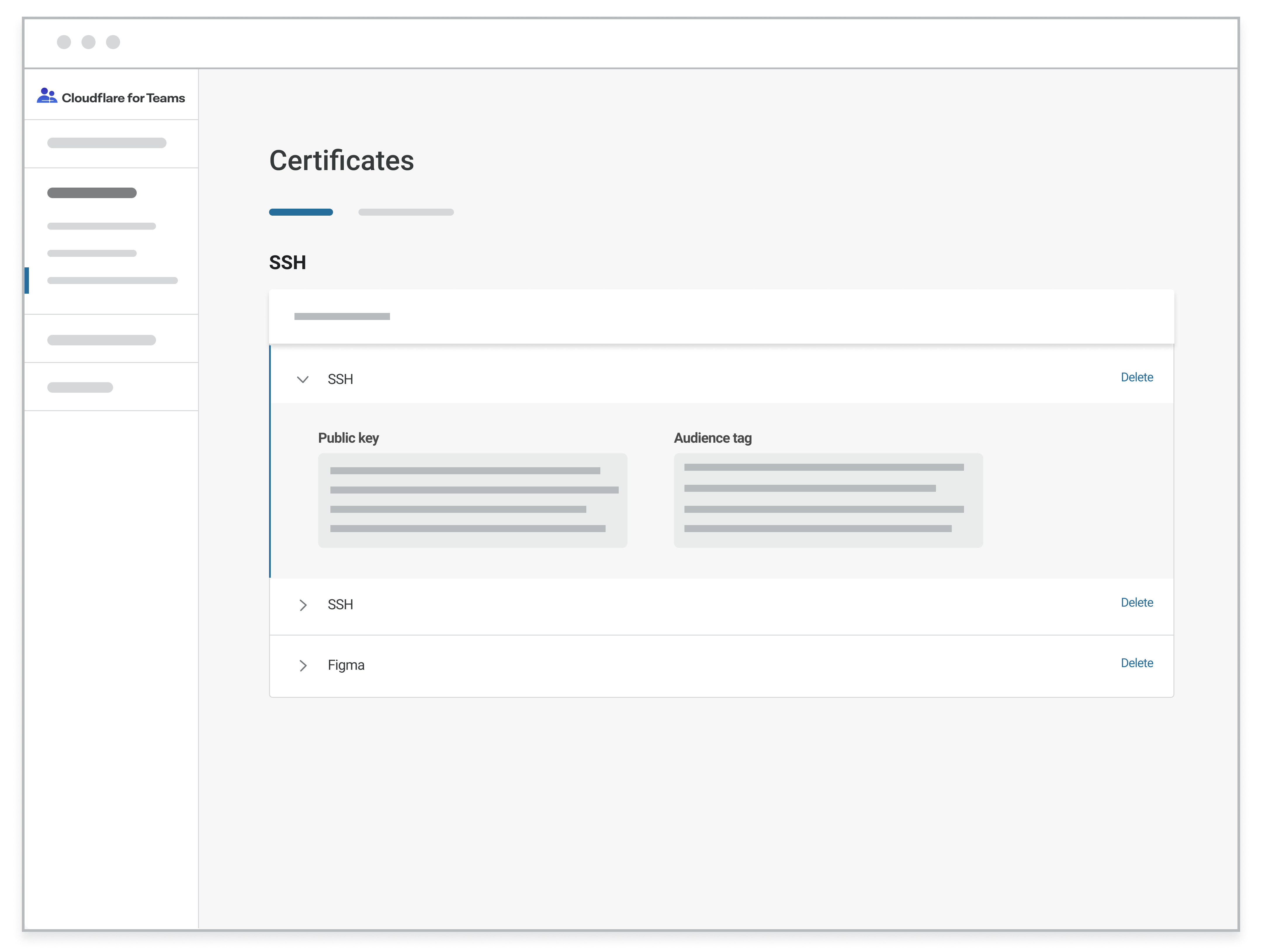
Accelerate DevOps workflows
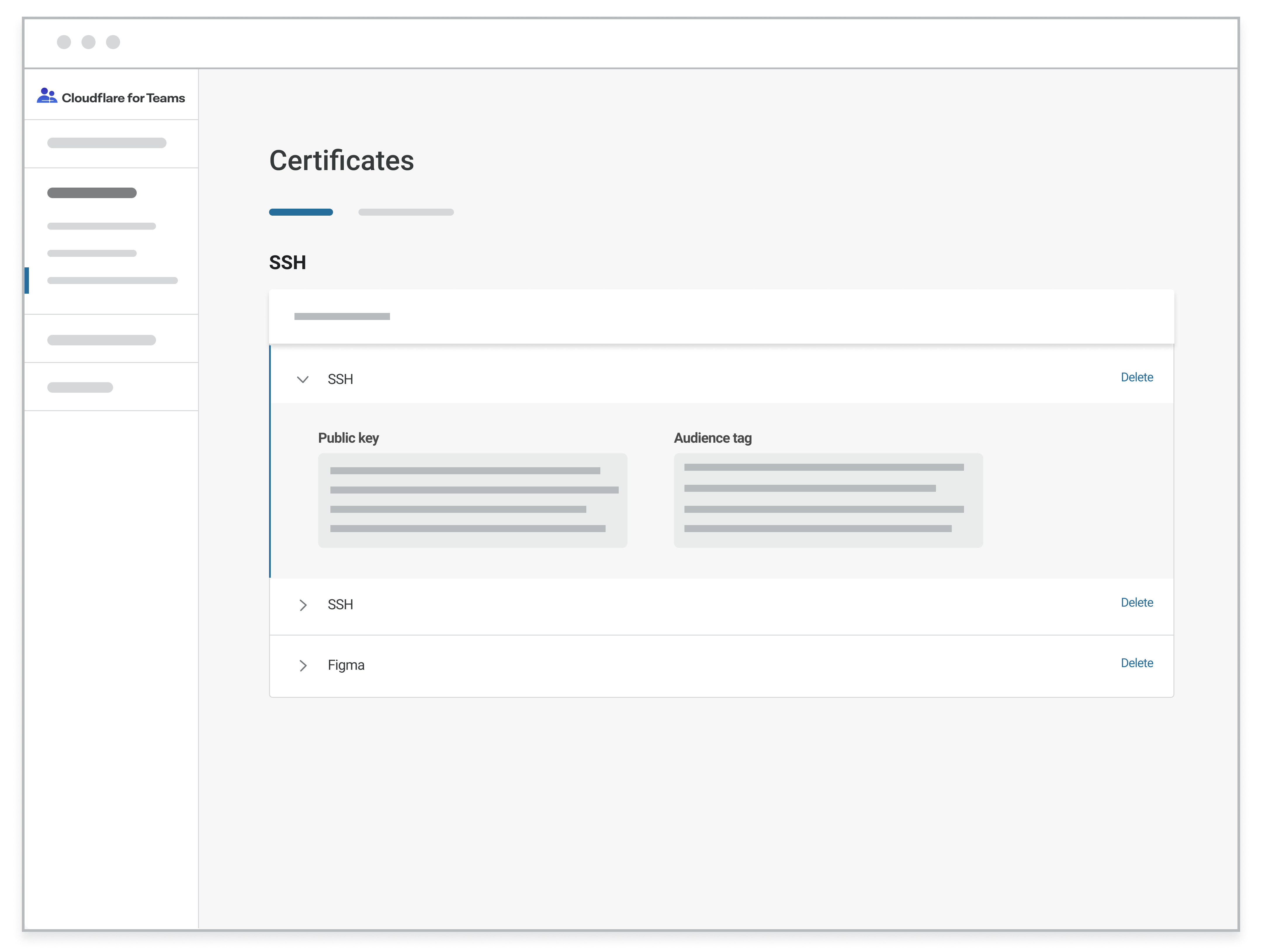
Engineers and related functions often need SSH access to your infrastructure to keep your business moving - and they don’t like to be slowed down. ZTNAs allow privileged technical users to access your critical infrastructure remotely - without experiencing tradeoffs.
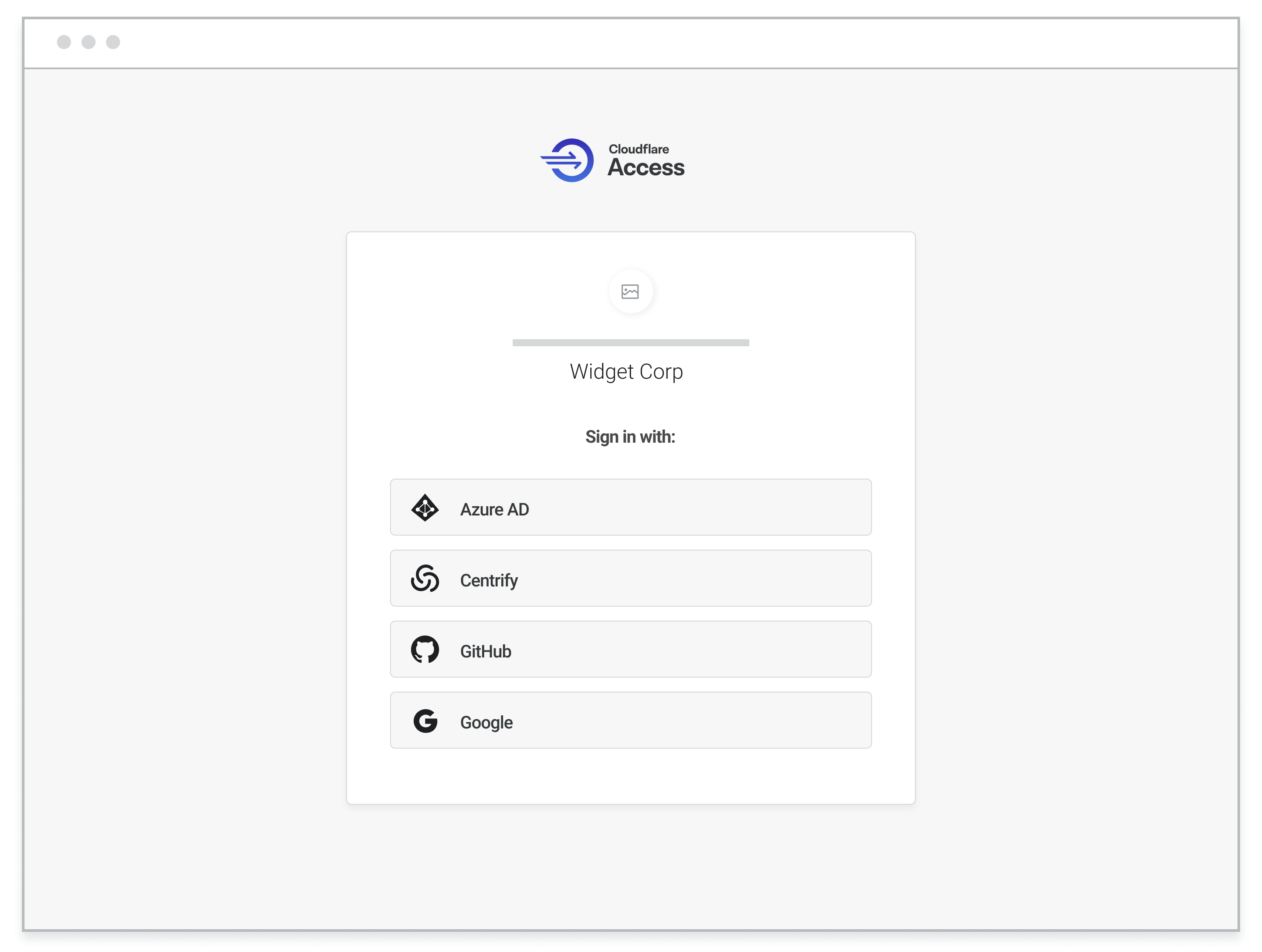
Give every user seamless authentication - even contractors and partners
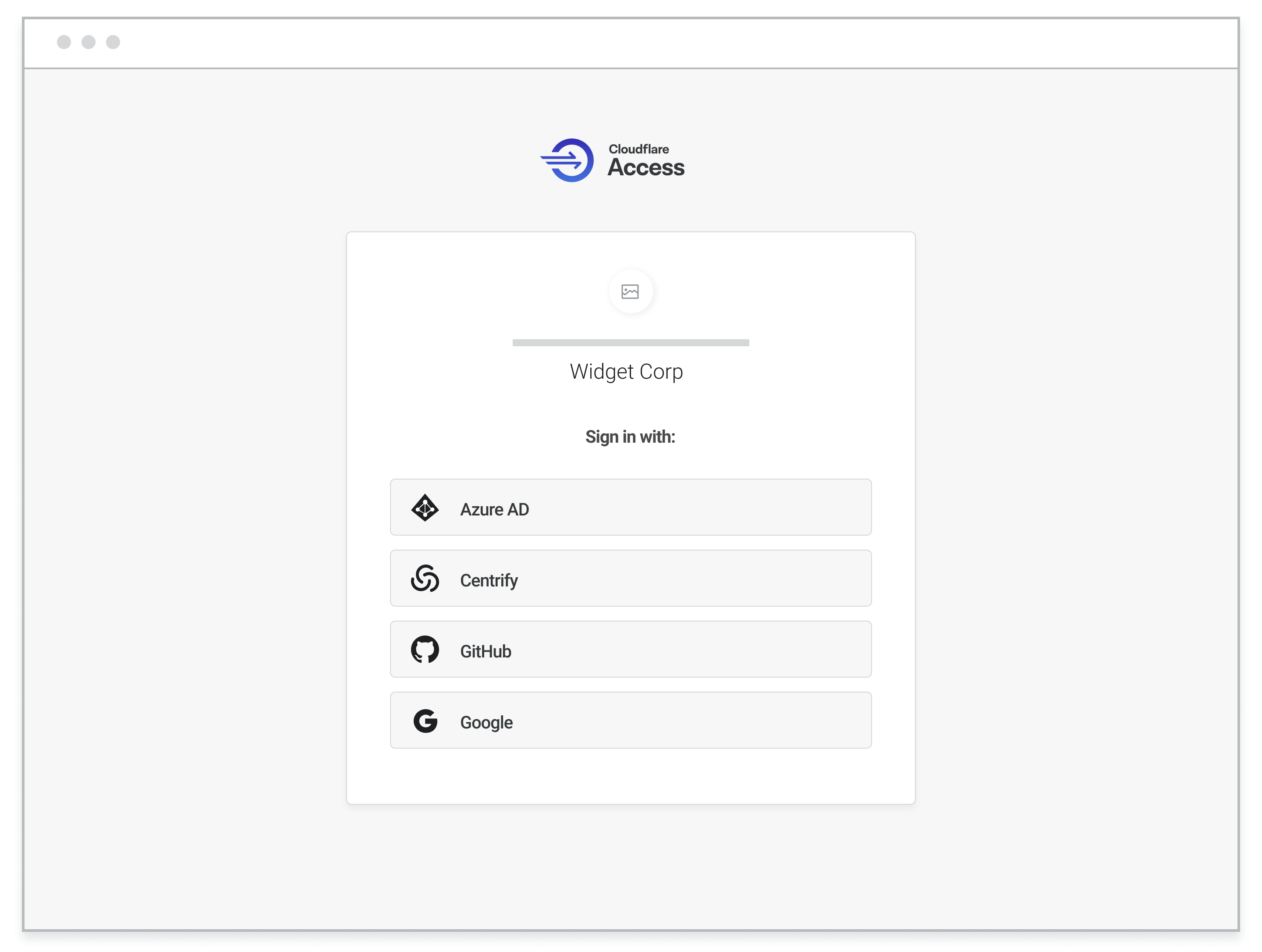
ZTNA saves room in your corporate directory by simultaneously integrating with multiple identity providers. External users can authenticate with a broad variety of corporate or personal accounts and still benefit from the same ease-of-use available to internal employees.
Start Now
Secure access to your corporate applications without a VPN. Getting started with Access takes minutes. With our free plan, your first 50 users are free.